Monitoring Screen Overview
This page explains the monitoring screen of the message authentication plugin. On this screen, you can check real-time TX/RX status of security messages and per-ID settings.
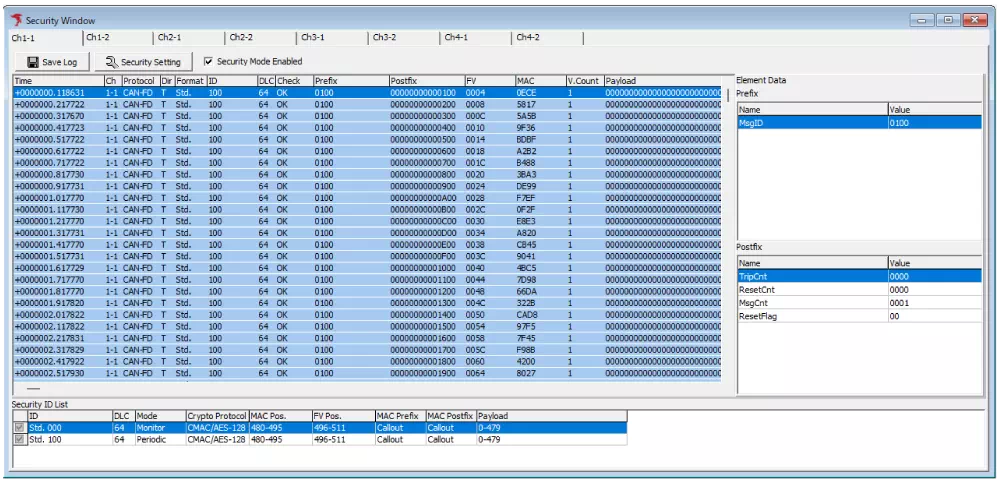
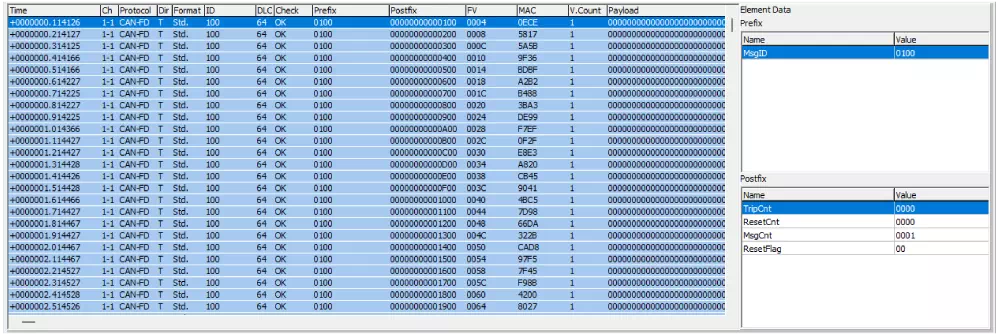
Security Message Log
Security Message Log lists all transmitted and received security-related messages. You can check when, on which channel, what message, and whether authentication succeeded.
- If communication or authentication fails, you can quickly identify ID, time, and cause.
- Useful for tracing state changes by message during security verification and log analysis.
| Category | Item | Description |
|---|---|---|
| Log area | Displays transmitted and received security messages. | |
| Time | Displays TX/RX timestamp. Format follows Time Stamp Form in Option dialog. | |
| Ch | Displays TX/RX channel. | |
| Protocol | Displays protocol type (CAN/CAN FD). | |
| Dir | Displays direction. T = transmit, R = receive. | |
| Format | Displays CAN ID type. Std. = standard ID, Ext. = extended ID. | |
| ID | Displays CAN ID. | |
| DLC | Displays data length. | |
| Check | Displays MAC verification result (OK/NG). OK = success, NG = authentication error. | |
| Prefix | Displays prefix value (hex). (*1) | |
| Postfix | Displays postfix value (hex). (*1) | |
| FV | Displays FV (Freshness Value). (*1) | |
| MAC | Displays authentication MAC value. (*1) | |
| V.Count | Displays MAC verification count. | |
| Payload | Displays payload value in data field. (*1) | |
| Element Data (*2) | Prefix | Displays prefix elements of selected security message in log area. (*3) |
| Postfix | Displays postfix elements of selected security message in log area. (*3) | |
1: Each field is displayed left-aligned in big-endian.
2: Hidden during monitoring.
3: Element Data is displayed as below and follows the Element Setting configuration.
| Item | Description |
|---|---|
| Name | Displays element name. |
| Value | Displays element value (hex), right-aligned in big-endian. |
Security ID List
Security ID List shows authentication parameters for all configured CAN IDs. You can quickly review security settings for each ID.
- Useful for bulk review when multiple IDs have different authentication settings or when misconfiguration is suspected.
- Quickly confirms which IDs have authentication enabled and whether settings follow operation rules.
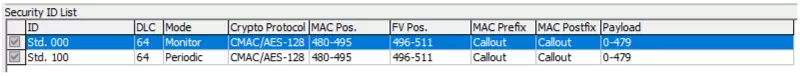
| Item | Description |
|---|---|
| ID | Displays configured CAN ID. Std. = standard ID, Ext. = extended ID. |
| DLC | Displays data length. |
| Mode (*1) | Displays message transmission mode: - Monitor: monitor-only message- Periodic: periodic transmission message (sends data frame at cycle configured in Target Frame Info Cycle) |
| Crypto Protocol | Displays cryptographic protocol used for MAC generation. |
| MAC Pos. | Displays bit position in data field where part of generated MAC is placed using Motorola sequential. Example: 40-63 means upper 24 bits of MAC are placed at bits 40 to 63 (D6 to D8). |
| FV Pos. (*2) | Displays FV bit position in data field using Motorola sequential. Example: 32-39 means FV is placed at bits 32 to 39 (D5). |
| MAC Prefix | Displays source of prefix value used in MAC calculation. (*3) |
| MAC Postfix | Displays source of postfix value used in MAC calculation. (*3) |
| Payload | Displays payload bit position in data field used as source data for MAC calculation, in Motorola sequential. Example: 0-31 means bits 0 to 31 (D1 to D4) are used as payload. |
1: Monitor mode is receive-only. Periodic mode transmits periodically.
2: Displays NotUsed when FV is not used.
3: Displays Callout when value from Callout DLL is used, otherwise NotUsed.